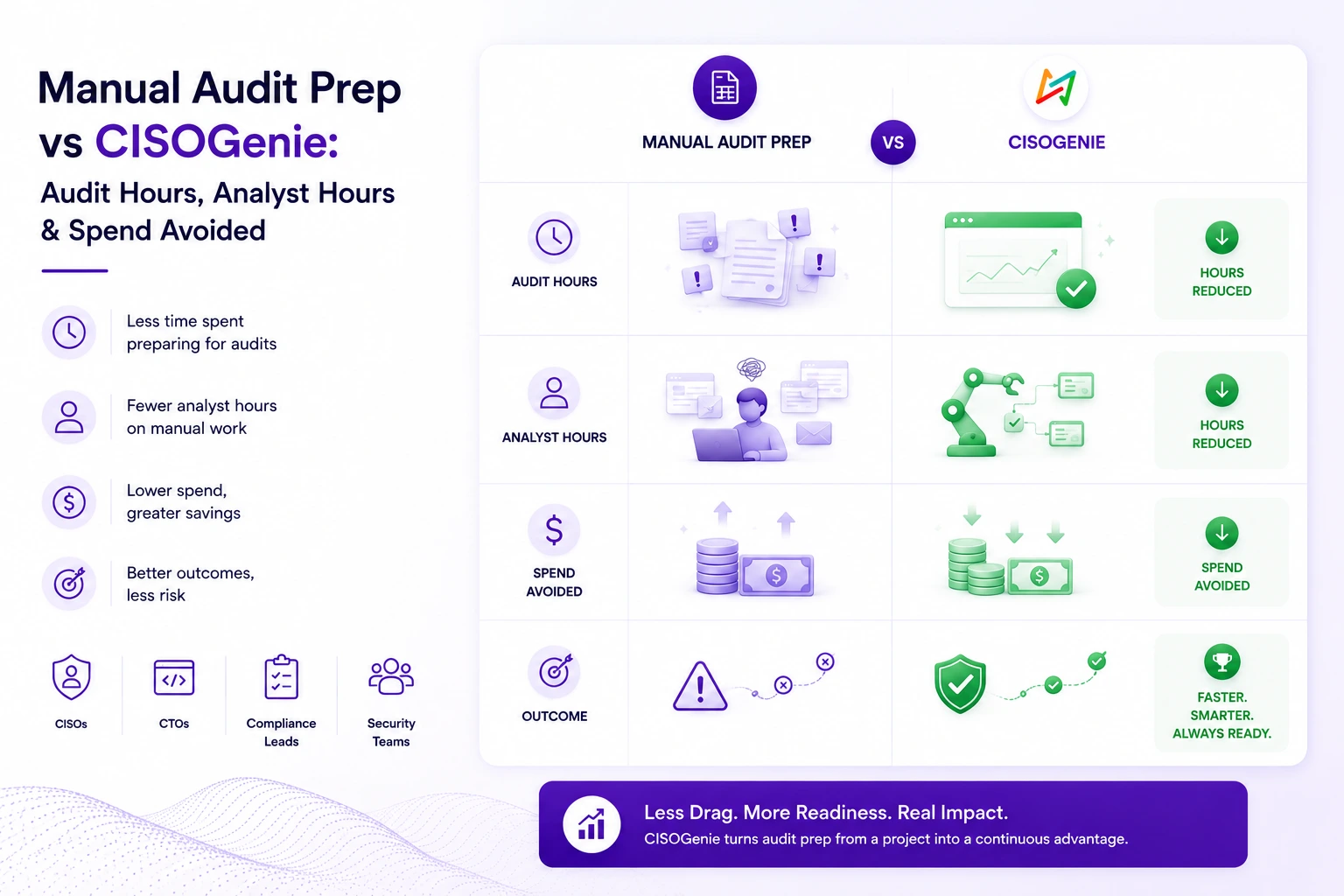
Manual Audit Prep vs CISOGenie: Audit Hours, Analyst Hours & Spend Avoided
The compliance teams that move fastest are not necessarily the largest. They are the ones that have removed the coordination drag sitting beneath the actual audit work — and replaced reactive preparation sprints with continuous operational readiness.
The Operational Problem
Audit readiness is not a checklist problem. It is a coordination and consequence problem.
Security teams preparing for SOC 2, ISO 27001, DPDPA, or a combination of frameworks consistently describe the same experience: by the time the audit window opens, weeks — sometimes months — have been consumed chasing evidence, resolving ownership questions, and fielding requests from auditors that were already answered in a previous cycle.
What is less often acknowledged is what that operational drag produces commercially. Delayed certification holds enterprise procurement in limbo. Stalled security reviews slow vendor onboarding. Customer trust cycles extend. Sales cycles lengthen. And leadership — watching audit preparation consume engineering, HR, legal, and security bandwidth simultaneously — often cannot get a clear answer about where readiness actually stands until the sprint is nearly complete.
None of this reflects poor judgment. It is the predictable result of audit preparation that was designed for one framework and one annual cycle — and has not been architecturally rebuilt as scope has grown.
"The audit itself is often not the bottleneck. Evidence readiness is. And when evidence readiness is a manual coordination problem, the consequences are not contained within the compliance team — they surface in deal timelines and board conversations."
Spreadsheet dependency at scale
Control registers, evidence trackers, task assignments, and remediation logs maintained across separate spreadsheets — each requiring manual reconciliation before each audit, with no shared state between cycles.
Repeated evidence collection cycles
Teams managing ISO 27001 and SOC 2 simultaneously collect overlapping evidence independently — because there is no shared control architecture to route that effort once across both obligations.
Fragmented ownership
Without a centralized system of record, control ownership lives in email threads and tribal knowledge. When auditors ask, that ambiguity resolves slowly — usually under deadline pressure.
Reactive preparation sprints
Many organizations begin structured audit preparation six to ten weeks before the audit window — because continuous readiness operations do not exist, and evidence is not maintained between cycles.
Consultant hours fill structural gaps
When internal systems are not configured for audit evidence traceability, organizations engage consultants to bridge the gap — a cost that recurs each cycle without changing the underlying architecture.
Leadership has no readiness visibility
CISOs and CTOs preparing board reports or responding to customer security escalations have no operational view of readiness between audits. "Where do we stand?" requires assembling an answer, not surfacing one.
Why Audit Preparation Takes So Long
The operational realities beneath long audit timelines.
Organizations preparing for their first major audit — or their fifth — consistently underestimate how much coordination time sits beneath the actual compliance work. The following reflects what audit preparation typically involves operationally, and why it expands beyond initial project estimates.
Evidence does not exist in one place
Audit artifacts — system configurations, access logs, policy documents, vendor contracts, training records, incident reports — live across teams, tools, and platforms. Collecting them requires reaching across engineering, HR, legal, and operations. That coordination layer is invisible in project timelines until it is not.
Control ownership is rarely documented at the execution level
Many organizations have a policy framework. What is often missing is ownership of individual controls at the operational level — who maintains the evidence, who validates the control is working, who escalates gaps before the audit window opens. That ambiguity resolves slowly, usually when the timeline is already tight. For CISOs managing board-level reporting, this creates a secondary problem: readiness status cannot be communicated with confidence if ownership itself is unclear. The compliance team is presenting an estimate, not a position.
Policy management is disconnected from operational controls
Policies need to be reviewed, versioned, and approved. When that lifecycle is manual — tracked in shared drives without traceability — audit teams spend disproportionate time reconstructing evidence that policy governance happened, rather than demonstrating it continuously. Auditors notice the difference.
Remediation tracking lives outside the compliance record
Gap assessments surface issues. Tracking their resolution — who owns the fix, what the timeline is, whether closure evidence maps back to the relevant control — typically happens in project management tools not integrated with the compliance record. The result is a second reconciliation problem that surfaces at the worst possible time: two weeks before the audit window.
Each framework is treated as a separate workstream
Organizations running ISO 27001 and SOC 2 simultaneously — or adding DPDPA to an existing program — often maintain separate evidence collections for each. The control overlap is substantial. Without a shared control architecture, the same evidence is requested, gathered, and maintained in multiple places by the same team.
Enterprise sales cycles feel the delay before the CISO does
Enterprise procurement increasingly requires certification before commercial terms are finalized. When audit preparation is reactive — starting six to twelve weeks before the audit window — organizations cannot respond to customer security requirements on a timeline that supports deal velocity. The compliance backlog becomes a sales constraint. That conversation eventually reaches executive leadership, and the answer is rarely satisfying.
Executive & Leadership Visibility
What manual audit preparation looks like from the governance layer.
Most compliance platforms are built for the analysts executing the work. CISOGenie is built for the full governance layer — including the CISOs and CTOs who need to report on readiness, anticipate audit risk, and make resource decisions without waiting for a quarterly evidence sweep to tell them where things stand.
The gap between operational execution and executive visibility is itself a governance problem. When readiness cannot be summarized without assembling a status report, leadership operates on delayed information — and that delay surfaces in board discussions, customer escalations, and regulatory interactions at exactly the moments when confidence matters most.
For CISOs
Board-facing readiness confidence. A continuous compliance dashboard means audit posture is always quantifiable — not assembled manually before each board meeting. CISOs can speak to open gaps and remediation progress from operational data, not informal team updates compiled the day before.
For CTOs
Governance oversight without engineering drag. Engineering teams are pulled into manual audit preparation more than anyone plans for. Structured evidence workflows reduce those unplanned interruptions — and give CTOs visibility into where cross-functional compliance dependencies actually sit before they become a sprint disruption.
For Compliance Leads
Readiness tracking across frameworks and teams. Instead of assembling readiness status from multiple spreadsheets and Slack conversations, compliance leads have a centralized operational record — control status, evidence completeness, remediation progress — across all active frameworks simultaneously.
For Executive Leadership
Audit posture visibility — without escalation. Leadership uncertainty about audit readiness is most acute in the weeks before an audit window. CISOGenie changes the timeline of that uncertainty. Readiness is visible continuously — not only when a preparation sprint surfaces what is missing.
Operational Comparison
| Operational Area | ⚠ Manual Preparation | ✦ CISOGenie Workflow |
|---|---|---|
| Initial gap assessment | Weeks of manual framework mapping; often requires consultant involvement to establish a credible baseline — and is repeated each cycle | Structured gap assessment against pre-mapped frameworks; control gaps visible from day one across ISO 27001, SOC 2, DPDPA, and others; maintained continuously between cycles |
| Evidence collection per control | Manual requests across engineering, HR, legal, and operations; evidence arrives in varied formats; gaps discovered late under audit deadline pressure | Connected evidence workflows with ownership assignment, deadline tracking, and format consistency; collected continuously — not assembled reactively before each audit window |
| Executive readiness reporting | Status assembled manually before board meetings or customer escalations; no operational view between audit cycles; leadership cannot report with confidence between windows | Continuous compliance dashboard — control status, evidence completeness, and audit posture visible to leadership at any point in the cycle without manual assembly |
| Policy lifecycle management | Policies in shared drives; version history informal; approval chains tracked in email with no traceability into the compliance record | Policy lifecycle with version control, approval workflows, and audit-ready traceability — linked directly to the controls they govern |
| Remediation tracking | Gap findings in project management tools disconnected from the compliance record; closure evidence not formally linked back to controls; late-cycle reconciliation required | Remediation workflows connected to control record; closure evidence captured and mapped; audit trail maintained without manual reconciliation |
| Cross-framework evidence reuse | Evidence collected separately per framework; duplicate collection common across ISO 27001, SOC 2, DPDPA, and sector-specific requirements | Shared control architecture routes evidence once across applicable frameworks; overlap identified structurally — not discovered during a parallel audit sprint |
Timeline and effort differences vary with audit scope, number of frameworks, organizational evidence maturity, and auditor requirements. The above reflects directional operational differences — not guaranteed outcomes.
Analyst Coordination Hours
Where analyst time actually goes during audit preparation.
| Coordination Area | Manual Preparation — Where Hours Go | CISOGenie Workflow — Where Hours Go |
|---|---|---|
| Evidence requests and follow-up coordination | High — recurring each cycle | ✔️ Substantially reduced |
| Spreadsheet maintenance and version reconciliation | Significant — manual overhead | ✔️ Real-time, not point-in-time |
| Cross-team coordination and ownership resolution | High — often unplanned | ✔️ Visible, assigned, tracked |
| Duplicate work across parallel frameworks | Additive — often unrecognized | ✔️ Structural reduction |
| Executive readiness reporting | Recurring — before each event | ✔️ Available on demand |
"In practice, this usually becomes a cross-functional operations problem. Engineering is pulled in for configuration evidence. HR for training records. Legal for contracts. Each touchpoint adds coordination latency — and that latency multiplies across frameworks and audit cycles without anyone making an explicit decision to accept it."
Consultant Dependency & Spend
Reducing the structural dependency on external audit support.
| Area | ⚠ Common Consultant Engagement Patterns | ✦ Where CISOGenie Changes the Dependency Structure |
|---|---|---|
| Gap assessment | Gap assessment repeated each cycle — because internal gap records are not maintained continuously between audits | Continuous gap assessment against 40+ frameworks — internal teams maintain their own readiness record without external reassessment each cycle |
| Evidence coordination | Evidence coordination — because control ownership and evidence location are not formally documented internally | Evidence ownership formally assigned and tracked — reduces unplanned coordination and last-minute evidence requests |
| Framework interpretation | Framework interpretation — because internal teams lack structured access to control libraries and cross-framework mapping guides | Pre-mapped control libraries across ISO 27001, SOC 2, DPDPA, DORA, RBI CSF, and more — framework interpretation accessible operationally |
Note: Consultant engagement remains appropriate for complex framework interpretation, scoping decisions, or mature audit program design. CISOGenie is not a substitute for human compliance judgment — it is the operational infrastructure that makes that judgment less expensive to apply, and less dependent on external support for activities that can be internalized.
Evidence Collection Architecture
Manual evidence workflows vs. connected evidence operations.
Manual
Step 01
Sequence
Auditor or internal team issues evidence request list
Manual
Step 02
Sequence
Compliance lead distributes requests manually
CISOGenie
Step 01
Sequence
Controls mapped with evidence requirements and ownership
CISOGenie
Step 02
Sequence
Evidence tasks orchestrated and collected continuously
Multi-Framework Duplication & Evidence Reuse
Managing overlapping compliance obligations without duplicating the work.
Illustrative Control Overlap — Select Framework Pairs
ISO 27001 ↔ SOC 2
High overlap
ISO 27001 ↔ DPDPA
Significant overlap
SOC 2 ↔ DPDPA
Moderate-high overlap
ISO 27001 ↔ DORA
Significant overlap
ISO 27001 ↔ RBI CSF
Moderate-high overlap
Operational & Executive Visibility
A compliance dashboard that reflects actual operational state.
Control status and evidence completeness
Live visibility into which controls are satisfied, which have incomplete evidence, and which carry open remediation items — across all active frameworks simultaneously, without manual aggregation.
Asset inventory and risk register
Risk-led view of assets, their classification, associated controls, and risk status — giving teams an operational basis for prioritization rather than proximity to the next audit window.
Evidence traceability system
Every piece of evidence linked to the control it supports, the framework it satisfies, and the owner responsible for maintaining it — full traceability without manual reconstruction at audit time.
Task orchestration across teams
Compliance tasks assigned to owners across engineering, HR, legal, and operations — with status tracking, deadline visibility, and escalation paths maintained in the platform, not in someone's inbox.
Risk-Led Differentiation
| Checklist-driven compliance | Risk-led compliance operations |
|---|---|
| Controls tracked as binary: implemented or not. Resources allocated based on what is outstanding, without weighting by business risk exposure. Remediation driven by audit proximity. | Controls evaluated in the context of the risks they address. The risk register informs remediation prioritization. Evidence collection structured around controls that carry the highest exposure if inadequate. |
| Leadership visibility requires a manual status sweep — and usually arrives too late to change anything. | Operational governance continuous — gaps addressed as part of normal operations, not concentrated into a pre-audit sprint. Leadership has real-time readiness visibility without requesting it. |
Business Impact of Delayed Readiness
Delayed enterprise procurement
Enterprise procurement increasingly requires SOC 2 or ISO 27001 certification before commercial terms are finalized. When certification timelines are uncertain, deal timelines are uncertain.
Stalled customer security reviews
Enterprise customers run their own vendor security reviews — often outside the scheduled audit window. Organizations without continuous compliance operations face these reviews reactively.
Slower vendor onboarding
Vendors that cannot demonstrate current compliance posture — or require weeks to respond to security questionnaires — are increasingly deprioritized in enterprise onboarding queues.
Extended sales cycles
Every additional week a certification takes — or a security questionnaire requires to answer — adds duration to enterprise sales cycles.
Readiness, Revenue & Customer Trust
Faster time to certification
Structured audit readiness operations reduce the pre-audit sprint. Organizations already maintaining evidence continuously enter audit windows with substantially more in place — and exit them faster.
Compliance as a sales asset — not a sales delay
A maintained compliance operations record — not just a point-in-time certificate — lets sales teams answer customer security questions with operational depth.
Faster expansion into regulated markets
Organizations with a multi-framework compliance infrastructure can extend into new regulatory environments without rebuilding from scratch.
Platform Capabilities
What CISOGenie delivers operationally.
- 40+ pre-mapped frameworks: ISO 27001, SOC 2, DPDPA, DORA, RBI CSF, SEBI CSCRF, GDPR, IEC 62443, ISO 42001, Essential Eight, CPS 234, Saudi PDPL, and more
- Connected evidence collection with ownership and deadline tracking
- Asset inventory and risk register — risk-led control prioritization
- Multi-tenant GRC SaaS and MCP-ready agentic AI workflows
A Note on Operational Realism
Automation supports compliance. It does not replace compliance judgment.
CISOGenie reduces the operational overhead of audit preparation — evidence collection, coordination, traceability, cross-framework management, and leadership reporting. It does not eliminate the need for human compliance judgment, auditor engagement, or organizational accountability for whether controls are actually implemented and maintained.
- Audit scope and timelines vary by framework and auditor
- Not every control can be automated — human judgment remains essential
- Audit-ready does not automatically mean certified
- The platform reduces coordination overhead — teams retain full operational control
Frequently Asked Questions
Evaluate Your Audit Readiness Architecture
A walkthrough of CISOGenie is structured around your specific situation — your active framework obligations, your team's current evidence workflow, and where the coordination overhead is actually concentrated.